At RSA, Dell’s SecureWorks launched two new offerings aimed at detecting intrusions. One is a hosted solution that offers new, managed end-point detection, and the other is a series of scripts and small programs that offers a clever way of detecting intruders. The newly available product is called AETD Red Cloak (for “Advanced Endpoint Threat Detection”), and it collects endpoint information before sending it to Dell’s cloud (securely) for evaluation and correlation. The other solution, called DCEPT, or “Domain Controller Enticing Password Tripwire,” is available, along with instructions, on GitHub here, and it’s designed to detect credential-scraping attacks that are normally very hard to detect.
Yet More Endpoint Tools?
Why the attention on new endpoint tools for what is surely a crowded vendor space? In the last year, Dell’s intrusion analysts noted that in most of the breaches they investigated, cyber intrusions occurred by gaining compromised credentials, and the attackers used little or no malware to accomplish their objective. Hackers used normal administrator tools and system software to move around and exfiltrate data.
Traditional security solutions, such as IPS/IDS, firewalls and antivirus, are of little use when the hackers don’t employ malware, or use it so sparingly that it leaves no Indicators of Compromise (IoC). Detecting this aberrant use of normal tools and techniques requires more data and a deep understanding of what is normal. Red Cloak has multiple modules that collect very detailed information, sending it to Dell for correlation with other endpoint data, information collected across the network, and observed trends across SecureWorks’ customer base.
Attackers’ sophistication means that defenders have to redefine winning in the enterprise. No longer is winning about keeping the attackers out, but about keeping attackers from their goal. That prize is usually exfiltrating data or other system compromise. Defense in depth strategies require not only mitigation to deter and prevent intrusions, but also instrumentation, to detect when an attack occurs. Credential-scraping attacks are hard to detect because often the only indicator is perhaps a suspicious pattern of network logons.
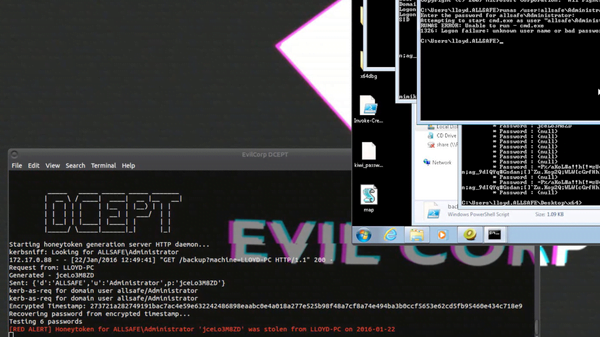
Dell’s DCEPT is based on honeytokens, a tripwire that reveals when an attack is taking place and when the honeytoken is accessed or used. If a domain Admin logs on to a local box with their credentials, those credentials are stored in a credential cache. With local admin privileges, Mimikatz or similar hacking tools can read the password or its hash and grant the attacker full network control. When accessed, a honeytoken credential sends an alert.
DCEPT, Domain Controller Enticing Password Tripwire
DCEPT came about when its authors, part of Dell’s CTU (Counter Threat Unit) Research, were thinking about how AD attacks are made and defenses against Mimikatz. They observed a key linein a SANS blog about how easy it is to cache fake credentials in memory by using run as as a tool. Most attackers will use Mimikatz to dump memory of a compromised system and use (a) token(s) in an attempt to escalate privileges. That’s because privileged local users can extract Windows login credentials cached by default in memory. If a domain administrator logs in to a compromised workstation interactively, their password is stored in the credential cache. What if one of those credentials extracted by an attacker was fake, was changed daily, and was unique to each workstation? If implemented as a honeytoken, we would know when and where that credential was compromised.
James Bettke and Joe Stuart, the DCEPT authors, described DCPET as consisting of three components: They wrote a few shell scripts for a monitor, a python .scr to act as server, and an agent to run run as. Initially this agent was written as a batch script, to interact with the password, but it’s now written in C# and caches honeytokens in memory on the endpoints. By extracting the API call for this logon process, the agent doing credential caching is better hidden in the background.
The second component is a server that generates and issues honeytokens to requesting endpoints. Generated tokens are stored in a database with the endpoint ID that requested the token and timestamp, thus facilitating forensic analysis. The third component acts as a monitor that listens passively for logon attempts. The DCEPT interface needs to be on the same network as the Domain Controller (DC) in order to capture packets. (The necessary docker container for the server is also on GitHub.)
 The DCEPT interface
The DCEPT interface
At the DC, the server watches for the Kerberos pre-authentication packet. In the pre-authenticated packet is the encrypted timestamp with credentials. An alert is generated when someone tries to authenticate with the encrypted honeytoken password. Comparing that encrypted credential to a list of generated passwords lets the defender know what workstation was initially compromised, even if the credential is used elsewhere.
AETD (Advanced Endpoint Threat Detection) Red Cloak
Dell’s CTU experts were very concerned with attack persistence in their cases. Red Cloak was developed to help their on-scene experts do proactive targeted threat hunting and serve as a force multiplier for IR (Intrusion Response) efforts. Red Cloak has been used by Dell for the past four years and has been placed on over 3.6 million endpoints. Clients supposedly clamored for continued assistance after finished engagements, so Red Cloak (RC) as a managed service is now offered.
In one case, within 48 hours of deploying RC, evidence of a compromise that had existed for 14 months was discovered. In another case, after an IR investigation of a small hotel chain, Dell, by using RC, was able to identify the same tactics being used at a much larger hotel chain. RC is not dependent upon any single indicator, behavior or malware signatures, but combines Threats, Tactics, and Procedures and is constantly learning from new clients.
After finding and eradicating the intruder, one must maintain vigilance post-eviction. Phil Burdett, of Dell CTU Special Operations, told Tom’s IT Pro a very important principle: “If you do not catch an attacker’s re-entry attempt, you likely missed a successful attempt.”
RC Details
RC, consisting of different modules appropriate to the scenario, is installed on a client’s endpoints, and information collected is sent to the cloud SaaS location over mutually authenticated connections. The average amount of information transferred per day from each endpoint is approximately 10 MB (compressed), and the service run as a low priority process and is therefore preempted for any user activity on the workstation. You may set memory or disk space capacity limits.
 The Red Cloak portal interface, showing health, endpoints, and status.
The Red Cloak portal interface, showing health, endpoints, and status.
Sometimes you need to find a needle in a haystack, but a solution such as RC makes that possible. According to Mr. Burdett, in over 50% of Dell’s espionage cases, the attackers used all or mostly native tools: PowerShell, net commands, and/or wmi. Living off the land – using native tools to do all or most of the attacker’s machinations – makes detection impossible for some tools and extremely labor intensive with other tools.
What is RC actually doing? RC detects any new processes and its arguments – say, spawning a new command shell; any persistent programs, especially those surviving a restart; anything that injects into LSAS spaces; signatures of tools residing in memory; mapping network drives with explicit credentials; memory allocation; and so on.
One specific module, codenamed Groundling (Dell would not confirm that this module was named after the Los Angeles comedy troupe, but neither would they deny it), was described “like Sysinternals’ (Microsoft) AutoRun on steroids.” This module provides RC with key details on Windows services, such as when run registry keys are set to point to a binary on disk, when DLL search order changes, or when DLL side-loading occurs. For example, an unsigned svc hosted service running out of a temporary directory would be classified as anomalous by groundling. Other modules detect behaviors and process changes such as deployment of subliminal web shells to web shells, or sysadmin use of BITS (Background Intelligent Transfer Service).
Summary
For a defender to be successful, they first have to find the intruder. Detection capabilities may be grouped into three classes:
- Tactical – where there is pre-knowledge of the type of attack, such as signature-based detection
- Strategic – where there is no pre-knowledge, but modules like groundling gather information to look for IoC (i.e., clearing of windows security event logs)
- Behavioral – this is the RC differentiator, where windows events are parsed across the enterprise and analyzed
RC is available now, starting at less than $100 per workstation per year. This includes the monitoring and technical support.
Dell’s secret sauce is in the analysis. You don’t need to detect just one thing or even everything; it’s the overall pattern. Dell SecureWorks’ experience with sophisticated threat actors, such as 3390and Gameover Zeus, means that the knowledge of how adversaries move, steal credentials, enumerate the network and attempt exfiltration is tied to RC analysis of endpoint data. This leads to much better threat alerts, and a much quicker kill chain.
[Source:- Tomsitpro]
